Ranking Government Secretism
Government cybersecurity "secretism," also known as the "Protocol of Silence," is a systemic institutional strategy where state-level entities intentionally hide, minimize, or obfuscate details regard...
14 Huhti 6min

Por qué los gobiernos ocultan los hackeos
El "secretismo" gubernamental en ciberseguridad, también conocido como el "Protocolo del Silencio", es una estrategia institucional sistémica en la que las entidades estatales ocultan, minimizan o con...
14 Huhti 19min
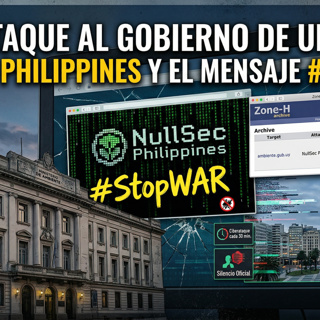
Digital Silence: Threat Intelligence vs. State Response in the #StopWAR Incident
The hacktivist attack by NullSec Philippines is currently considered a "classic low-impact hacktivist defacement" that is "embarrassing but not catastrophic" for Uruguay's public sector. The immediate...
13 Huhti 8min

Un Hackeo que Nadie Notó
NUEVO VIDEO: Un Hackeo que Nadie NotóEl grupo hacktivista "NullSec Philippines" logró vulnerar el sitio web del Ministerio de Ambiente de Uruguay y un sistema de declaraciones juradas, dejando archivo...
13 Huhti 1min
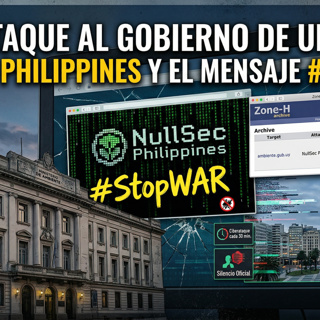
Ciberataque al Ministerio de Ambiente de Uruguay
Descripción del Episodio:Descubre los detalles del reciente ciberataque contra el gobierno de Uruguay. En este episodio, analizamos cómo el grupo "NullSec Philippines" logró vulnerar el sitio web del ...
13 Huhti 1min

The Manual Override: Logic, Trauma, and the Digital Knight
The Manual Override: Logic, Trauma, and the Digital KnightEpisode Description:When trillion-dollar algorithms fail, and the machine dictates that your reality doesn't exist, how do you force a manual ...
13 Huhti 5min

The Analog Backdoor: How a Mother Hacked the Justice System
The Analog Backdoor: How a Mother Hacked the Justice SystemEpisode Description:In a world dominated by state-sponsored cyber warfare, trillion-dollar algorithms, and massive geopolitical cover-ups, th...
13 Huhti 4min

The Narrative Hijack: The Alberto Hill Story
2. Radical Transparency as a WeaponThe Digital Dissident does not hide; he broadcasts. Hill uses "radical transparency" to counter the secrecy and incompetence of the state.Public Documentation: He do...
8 Huhti 6min