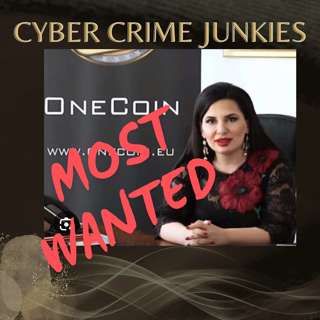
Rise And Fall of Crypto Star. FBI most wanted, Ruja Ignatova. Crypto News.
Crypto News, Cyber flash point about self-proclaimed Bitcoin killer, OneCoin. rise and fall of crypto star FBI most wanted, Ruja Ignatova. To Submit a TIP and Potentially collect the new $5 Million...
15 Maalis 202539min

Innovative Ways to Reduce Website Spoofing
After years in the industry, inventing and exploring emerging technologies, Gideon Hazam, Co-Founder, COO and CSM at Memcyco, https://www.memcyco.com/home found a way to solve a problem outside the no...
8 Maalis 202559min
Unmasking Invisible Threats: Quantifying Cyber Security
Rob Black, a security educator and Fractional CISO, joins us to discuss the best ways for quantifying cyber security and why it is crucial for small and medium-sized business owners. David Mauro int...
7 Maalis 20251h 4min
Phone Rings. It's A Social Engineer Callling.
Video Episode: https://youtu.be/oH7FpvHOhVA This is the story of Matt Smallman, author of “Unlocking Your Call Centre”, about how call centers can be security risks. Our discussion gives exclusive i...
1 Maalis 202558min
Quantum AI: What You Need to Know NOW!
Quantum AI: What You Need to Know NOW! 🚨🔐 Quantum computing is revolutionizing cybersecurity—are we ready? In this Cyber Crime Junkies episode, we uncover how quantum tech could break encryption, th...
28 Helmi 202532min
War Games. In Business.
This is the story of Lester Chng, CISSP and the Art of How To Use War Games In Business. Topics discussed: how to use war games in business, understanding war game exercises in business, leveraging wa...
28 Helmi 202546min

New Ways Leaders Can Assess Their Risk Appetite
In this conversation, Dan Elliott, principal cybersecurity risk advisor at Zurich, discusses new ways leaders can assess their risk appetite. KEY TOPICS: · how risk appetite effects your cyber s...
26 Helmi 202553min

Secrets Revealed--How To Grow Business Not Get Hacked🔥
🚨 New episode 🚨 host David Mauro engages with technology and security leaders to explore the critical roles of Network Operations Centers (NOC) and Security Operations Centers (SOC) in modern busine...
19 Helmi 202539min