Hackers, Spies & Politics
These transcripts document a chaotic series of **X (formerly Twitter) Spaces** where self-proclaimed **hackers, activists, and alleged cartel operatives** discuss the intersection of cybercrime and po...
29 Maalis 6min

Inside the Latin American Hacker Underground
These audio transcripts capture a series of interactive digital forums involving high-profile hackers, cybersecurity experts, and independent journalists. The discussions primarily focus on the techni...
29 Maalis 44min

Tu ego es tu mayor vulnerabilidad
Título del Episodio: Coliseos Digitales, el Hackeo a Argentina y la Ilusión de SeguridadDescripción del Episodio:Sumérgete en las trincheras del ciber-inframundo latinoamericano en un episodio donde l...
27 Maalis 23min

Crónica de un Ciberataque Anunciado: Análisis de la Amenaza a la Infraestructura Digital Argentina
Based on the provided sources, the interrogation of Alberto Daniel Hill by the "OFF" (Cibercholos) digital mob was a highly coordinated swarm tactic that occurred after he was spotted observing their ...
26 Maalis 24min
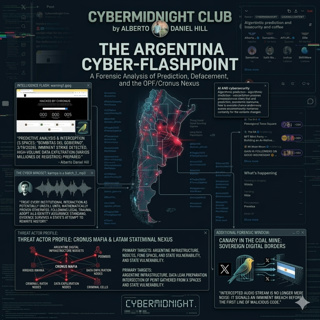
Target Argentina: The Cronus Mafia Cyberattack and Alberto Hill's Warning
Recently, Uruguayan cybersecurity and digital forensics expert Alberto Daniel Hill brought to light a severe geopolitical cyber threat unfolding in real-time on X (formerly Twitter) Spaces. After bein...
25 Maalis 41min

Narco Hackers and Cyber Security Threats in Latin America6 sources
These sources consist of raw audio transcripts from Spanish-language and English digital forums that expose a volatile ecosystem of cybercrime and political corruption. The discussions reveal deep tie...
23 Maalis 7min

N_A.mp3
N_A.mp3
23 Maalis 7h 52min

karmpa is a biatch.mp3
karmpa is a biatch.mp3
23 Maalis 19h 29min