Argentina: Una Historia de Hackers
De la Crisis al Ciberdelito: La Historia del Hacking en Argentina1. Introducción: El Nacimiento de una Cultura ÚnicaLa cultura hacker en Argentina no surgió en un laboratorio tecnológico ni en un prós...
16 Okt 20256min

Estudio de Caso: Anatomía de una Estafa Cripto con Deepfakes de Elon Musk
Estudio de Caso: Anatomía de una Estafa Cripto con Deepfakes de Elon Musk1.0 Introducción: El Advenimiento de las Estafas Potenciadas por IALas estafas en línea han evolucionado significativamente des...
16 Okt 20256min

La Trampa de Tinder
La Trampa de TinderThe sources present a composite study of the dangers of online dating and the emergence of an unconventional media platform dedicated to cybersecurity and digital advocacy. One set ...
16 Okt 20258min

La Crisis Digital de Uruguay
Un Análisis Exhaustivo de la Catástrofe Cibernética del Gobierno Uruguayo: Fallos Sistémicos, el Compromiso Fatal de 30.000 Certificados PKI de Identidad Nacional, y la Peligrosa Brecha entre la Ambic...
16 Okt 20258min

Uruguay's Digital Breach: A Crisis of Trust and Security
Analysis of Systemic Cybersecurity Failures in the Uruguayan GovernmentExecutive SummaryThis briefing analyzes a series of large-scale data breaches targeting Uruguayan government entities, which star...
16 Okt 20257min

Anonymous: We Are Legion. Expect Us.
Anonymous: We Are Legion. Expect Us.Dive into the chaotic world of Anonymous, the decentralized computer hacker group and serious political movement that became known as the "final boss of the interne...
16 Okt 20257min

The Strategic Paradox: Inside Peru's Escalating Cyber Crisis—From Hacktivism to RaaS Extortion
Title: The Strategic Paradox: Inside Peru's Escalating Cyber Crisis—From Hacktivism to RaaS ExtortionDescription:In this episode, we dive deep into the dramatic escalation of cyber threats gripping Pe...
16 Okt 20256min
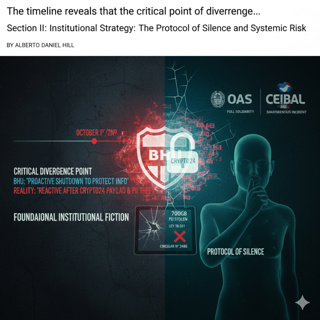
The Prophet and the Storm
The Prophet and the StormCybersecurity expert Alberto Daniel Hill delivers an unflinching analysis of the moment Uruguay’s celebrated reputation as a digital pioneer collapsed, arguing that the catast...
16 Okt 20256min