The Digital Scapegoat
Displaced aggression is a robust psychological phenomenon defined as the redirection of intense rage or hostility from its original source of provocation onto a substitute, often innocent, target. Thi...
9 Okt 20257min

Displaced aggression is a robust psychological phenomenon defined as the redirection of intense rage or hostility from its original source of provocation onto a substitute, often innocent, target
https://cybermidnight.club/deconstructing-the-attack-a-psychological-analysis-for-understanding-and-healing-2/Displaced aggression is a robust psychological phenomenon defined as the redirection of in...
9 Okt 202515min

The Calculated Cruelty of CyberGurl10: Displaced Aggression and the Weaponization of High-Trust Digital Space
These sources collectively provide a detailed psychological and legal analysis of a relational conflict where an individual, CyberGurl10, publicly attacked her fiancé, Alberto, in an online forum, con...
9 Okt 202537min

Crisis del BHU: Dos Narrativas
1. Introducción: Dos Crisis, Dos Relatos y una Verdad en DisputaLa reciente ola de ciberataques en Uruguay ha puesto de manifiesto no solo las vulnerabilidades técnicas de su infraestructura crítica, ...
9 Okt 20256min
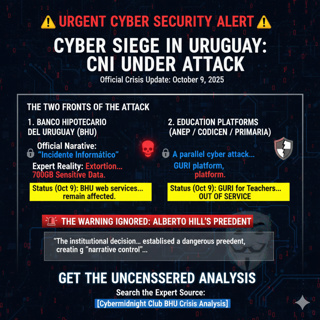
Cyber-Sovereignty Under Siege - Uruguay and BANCO HIPOTECARIO DEL URUGUAY
The latest update, which provides context and status as of October 9, 2025, significantly reinforces the core tenets of Alberto Hill’s counter-narrative, primarily by highlighting the systemic nature ...
9 Okt 20258min

Weaponizing Trust: Why a Public X Space Attack Was More Destructive Than Fighting a Lawyer and an Abusive Ex
HIIS THE ANSWER TO THE FOLLOWING MESSAGE OF CYBERGURL1'0 ON TWITTTER AFTER PUBLISHING AN ARTICLE BASED ON THE EVENT RELATED""And Im one with ager issues. Told there also that it was only way for me to...
9 Okt 202511min

Deconstructing the Attack: A Psychological Analysis for Understanding and Healing
Deconstructing the Attack: A Psychological Analysis for Understanding and HealingIntroduction: A Framework for Understanding What HappenedThis document provides a clear and objective framework for und...
9 Okt 20257min

Displaced Aggression and Relational Betrayal
Deconstructing the Attack: A Psychological Analysis for Understanding and HealingIntroduction: A Framework for Understanding What HappenedThis document provides a clear and objective framework for und...
9 Okt 202527min